What is DDoS mitigation?
Properly implemented DDoS mitigation is what keeps websites online during an attack. Explore the process of DDoS mitigation and the important characteristics to look for in a mitigation service.
Learning Objectives
After reading this article you will be able to:
- Explore mitigation strategies for DDoS attacks
- Learn about the range of DDoS attacks
- Highlight common attacks
Related Content
What is a DDoS attack?
What is a denial-of-service (DoS) attack?
DNS flood attack
Web application firewall (WAF)
Ping of death (historic)
Want to keep learning?
Subscribe to theNET, Cloudflare's monthly recap of the Internet's most popular insights!
Copy article link
What is DDoS mitigation?
DDoS mitigation refers to the process of successfully protecting a targeted server or network from a distributed denial-of-service (DDoS) attack. By utilizing specially designed network equipment or a cloud-based protection service, a targeted victim is able to mitigate the incoming threat.
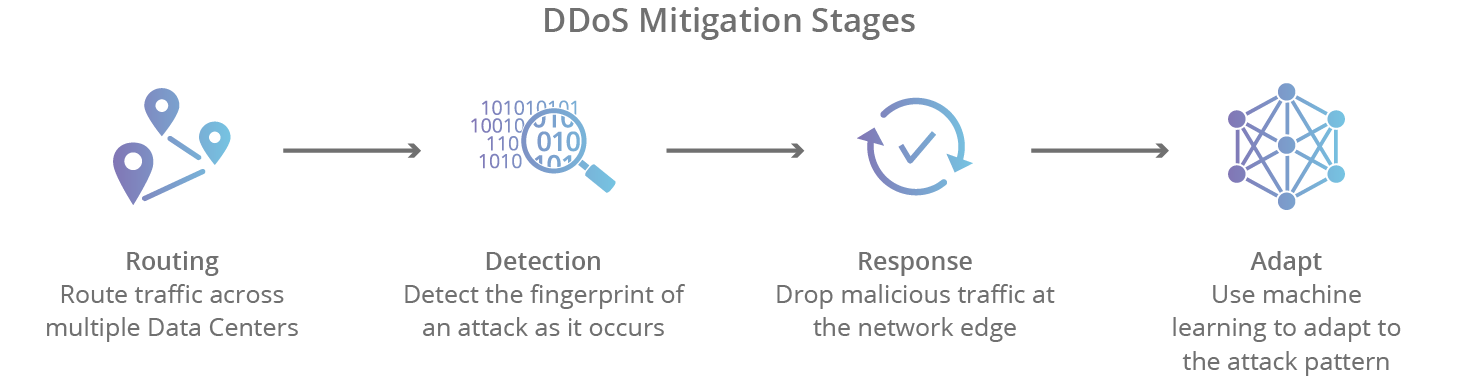
There are 4 stages of mitigating a DDoS attack using a cloud-based provider:
- Detection - in order to stop a distributed attack, a website needs to be able to distinguish an attack from a high volume of normal traffic. If a product release or other announcement has a website swamped with legitimate new visitors, the last thing the site wants to do is throttle them or otherwise stop them from viewing the content of the website. IP reputation, common attack patterns, and previous data assist in proper detection.
- Response - in this step, the DDoS protection network responds to an incoming identified threat by intelligently dropping malicious bot traffic, and absorbing the rest of the traffic. Using WAF page rules for application layer (L7) attacks, or another filtration process to handle lower level (L3/L4) attacks such as memcached or NTP amplification, a network is able to mitigate the attempt at disruption.
- Routing - By intelligently routing traffic, an effective DDoS mitigation solution will break the remaining traffic into manageable chunks preventing denial-of-service.
- Adaptation - A good network analyzes traffic for patterns such as repeating offending IP blocks, particular attacks coming from certain countries, or particular protocols being used improperly. By adapting to attack patterns, a protection service can harden itself against future attacks.
Choosing a DDoS mitigation service
Traditional DDoS mitigation solutions involved purchasing equipment that would live on site and filter incoming traffic. This approach involves purchasing and maintaining expensive equipment, and also relied on having a network capable of absorbing an attack. If a DDoS attack is large enough, it can take out the network infrastructure upstream preventing any on-site solution from being effective. When purchasing a cloud-based DDoS mitigation service, certain characteristics should be evaluated.
- Scalability - an effective solution needs to be able to adapt to the needs of a growing business as well as respond to the growing size of DDoS attacks. Attacks larger than 2 terabits per second (Tbps) have occurred, and there’s no indication that the trend in attack traffic size is downward. Cloudflare’s network is capable of handling DDoS attacks considerably larger than have ever occurred.
- Flexibility - being able to create ad hoc policies and patterns allows a web property to adapt to incoming threats in real time. The ability to implement page rules and populate those changes across the entire network is a critical feature in keeping a site online during an attack.
- Reliability - much like a seatbelt, DDoS protection is something you only need when you need it, but when that time comes it better be functional. The reliability of a DDoS solution is essential to the success of any protection strategy. Make sure that the service has high uptime rates and site reliability engineers working 24 hours a day to keep the network online and identify new threats. Redundancy, failover and an expansive network of data centers should be central to the strategy of the platform.
- Network size - DDoS attacks have patterns that occur across the Internet as particular protocols and attack vectors change over time. Having a large network with extensive data transfer allows a DDoS mitigation provider to analyze and respond to attacks quickly and efficiently, often stopping them before they ever occur. Cloudflare’s network runs Internet requests for millions of websites, creating an advantage in analyzing data from attack traffic around the globe.
FAQs
What is the primary objective of DDoS mitigation?
DDoS mitigation protects a network or server from a distributed denial-of-service attack. The goal is to keep a website or service online by dropping attack traffic and absorbing the rest of the traffic.
How does a DDoS protection service differentiate between an attack and a real visitor?
DDoS mitigation solutions use several factors to identify legitimate traffic, including common attack patterns, IP reputation, and historical data. This ensures that when a site experiences a surge of real visitors they are not accidentally blocked or throttled.
What are the key stages of a response to a DDoS threat?
Once a threat is identified, the protection network drops malicious bot traffic while absorbing the remaining traffic. An effective solution will also route traffic into manageable segments to prevent denial of service in the event of abnormal traffic volume.
Why is network size important when choosing a mitigation provider?
A larger network allows a provider to analyze data from millions of websites globally to identify changing protocols and attack vectors. Having an extensive data transfer capacity helps providers respond to and stop attacks more efficiently, sometimes before they even start.
How do cloud-based services handle large-scale volumetric DDoS attacks?
Scalable cloud solutions for DDoS mitigation are designed to handle large attacks that can exceed 2 terabits per second (Tbps). Unlike on-site hardware, which can be overwhelmed by large attacks that take out upstream infrastructure, cloud-based networks are large enough to absorb these massive volumes of traffic. Cloud-based DDoS mitigation also avoids the latency incurred by the use of scrubbing centers: remote data centers through which all network traffic must pass so that malicious traffic can be scrubbed.
What role does adaptation play in long-term DDoS protection?
A high-quality DDoS mitigation network constantly analyzes traffic to find attack patterns, such as specific protocols being misused or repeat offending IP blocks. By adapting to these patterns, the service can harden its defenses against future threats.
What features ensure a DDoS mitigation service is reliable?
Reliability is maintained through a combination of high uptime rates, redundancy, and a global network of data centers. Additionally, having site reliability engineers available 24 hours a day to identify new threats is essential for a successful protection strategy.